The business of collection of signals intelligence by the US evolved during and after the two world wars
 The business of collection of signals intelligence by the US evolved during and after the two world wars. The National Security Agency was formally created in 1952 to collect and analyse all signal intelligence globally. The Agency’s prime target was the Soviet Union and it worked closely with the British GCHQ. Having concentrated all its resources in covering the Warsaw Pact countries, the Agency seemed to have lost direction after the collapse of the Soviet Union. The adrenaline did not flow in the 1990s and after the September 11, 2001 terrorist attack, the NSA discovered that it did have information about the activities of many of the terrorists and their phone calls, but did not join the dots and share the information. Stung by this, the NSA began to collect all information, even from domestic American sources, without authorisation.
The business of collection of signals intelligence by the US evolved during and after the two world wars. The National Security Agency was formally created in 1952 to collect and analyse all signal intelligence globally. The Agency’s prime target was the Soviet Union and it worked closely with the British GCHQ. Having concentrated all its resources in covering the Warsaw Pact countries, the Agency seemed to have lost direction after the collapse of the Soviet Union. The adrenaline did not flow in the 1990s and after the September 11, 2001 terrorist attack, the NSA discovered that it did have information about the activities of many of the terrorists and their phone calls, but did not join the dots and share the information. Stung by this, the NSA began to collect all information, even from domestic American sources, without authorisation.

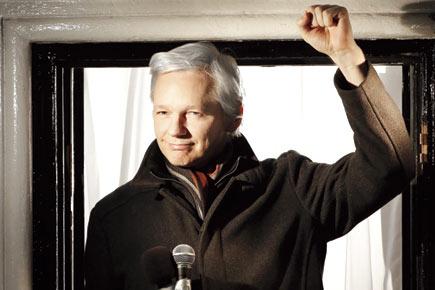
Intelligence leaks of the largest ever number of diplomatic and defence documents by Bradley Manning to Julian Assange of Wikileaks in 2010 created global furore and embarrassment. Pic/Getty Images
It is ‘America First’ in the business of collection of all source intelligence for the US. A country that maintains over a thousand bases of various categories all over the globe, has economic, trade and military interests all over, needs all time all spectrum intelligence to preserve its supremacy. This is backed by financial and technical resources. Its more than $500 billion defence budget is supported by an intelligence budget of 75 billion US dollars, which is more than India’s annual defence budget.
US intelligence activity is aided by the private industrial and technology houses like Boeing, IBM and SAIC. The process of intelligence collection and analysis has been privatised substantially. All information or data generated globally by phone calls, credit card receipts, social networks like Facebook, Myspace and Twitter, GPS tracks, cell phone geolocation, Internet searches, Amazon book purchases, Internet money transfers, etc, is gathered, in all languages. It is like a giant vacuum cleaner swallowing everything that comes its way. Mountains of data measured in peta and exabytes have been stored and hopefully processed into usable intelligence. In the 21st century, intelligence collection is far more complicated, urgent and often has to be in real time.
The extent of US intelligence surveillance activity was the best known secret in the intelligence world. In fact, detailed books have been written by American experts. A professional intelligence officer would not have been surprised with the disclosures about US eavesdropping on Indian political leaders. Intelligence leaks of the largest ever number of diplomatic and defence documents by Bradley Manning to Julian Assange of Wikileaks in 2010 created global furore and embarrassment. This had been followed by Edward Snowden’s disclosures in 2013 of the extent of NSA’s domestic and external surveillance, including the joint Anglo-American Project PRISM.
This project was really an upgrade of the earlier project ECHELON under which five intelligence agencies of the US, UK, Australia, New Zealand and Canada were also watching their NATO allies. PRISM did not exclude even snooping on the personal phones of presidents of friendly countries. Earlier this year, the CIA signed a $600 million deal with Amazon Web Services to develop a computing cloud, which will service all 17 American intelligence agencies to share services and information, leading to a new era of cooperation, and avoid the gaps and blind alleys that preceded the September 11, 2001 attacks.
India has had to deal with terrorism and conventional threats but our capacities to watch these threats are minuscule compared to US abilities. In a way, threats to India from terrorism and hostile neighbours are far more immediate. There is now the added problem of involvement of Indian youth in the terrorism of ISIS. The young get influenced sitting at home on their computers and physical human contact is no longer a prime requirement. Modern technology and communications have ensured this. No wonder the US has taken the route it has to preserve its national security. The difficulty with surveillance and collection of intelligence about terrorism, crime syndicates of gunrunners, human traffickers, narcotics smugglers, counterfeit currency dealers and hawala merchants, is that it is impossible to distinguish between internal and external threats.
Personal freedom, rights to privacy and individual rights are the essential ingredients of democracy. However, these have to be limited by another person’s freedom and rights. The state can ensure these only if it also provides security. This is the second limiting factor to freedoms and rights. The debate between the right to privacy and the need for the state to ensure safety of its citizens and other assets is going to be never ending as neither can overwhelm the other.
The writer is a former chief of Research and Analysis Wing (RAW)
 Subscribe today by clicking the link and stay updated with the latest news!" Click here!
Subscribe today by clicking the link and stay updated with the latest news!" Click here!